By Iulian Constantinescu, Levi9 DevOps Engineer
As a DevOps professional, I need to ensure smooth integration, continuous deployment, and uninterrupted operation of cloud infrastructures. As it gets more popular, the cloud brings vast potential with its countless services, presenting both an opportunity and a challenge. I was walking a tightrope between managing multiple accounts, ensuring compliance, and maintaining security standards across a growing infrastructure. Then I discovered the AWS Control Tower.
Manual operations led to consistency issues
Before the AWS Control Tower, managing AWS environments used to be tedious and time-consuming. To comply with security and compliance policies, each new account needed to be configured manually. When we scaled operations, our systems gained new capabilities and flexibility, but they also became more complex and more difficult to manage. As the project grew, it took more effort to ensure that every account adhered to best practices for security and governance.
Guardrail setup, compliance monitoring, and account provisioning were all manual processes that were open to human error and inconsistent results. We did not have a unified dashboard, which meant that we needed to switch back and forth to track the state of various environments. Our workflows were fragmented and inefficient.
AWS Control Tower proved to be a game-changer. AWS Control Tower is a service that offers an easy way to set up and govern a secure, multi-account AWS environment based on AWS best practices. It gave cloud operations the level of automation, standardization, and visibility I had been seeking for a long time.

AWS Tower key features
- Automated account creation: AWS Control Tower provides a straightforward way to set up and configure new AWS accounts through Account Factory. This feature allows me to quickly create new accounts that automatically comply with predefined security and governance policies. What once took me hours, now happens in a matter of minutes. The resulting configurations are consistent and reliable.
- Guardrails for security and compliance: One thing I like about AWS Control Tower is that it allows me to set guardrail preconfigured governance rules that help enforce policies and detect violations. The guardrails can be preventive, detective and proactive, providing two layers of security and compliance. This AWS feature ensures that all accounts are monitored and aligned with organizational policies, without requiring my manual intervention.
- Centralized management: AWS Control Tower offers a unified dashboard that shows all the AWS accounts in one tab. With the centralized management console, I can quickly assess what the account compliance status is, enable and disable guardrails, and have quick access to audit reports. The dashboard transformed the way I monitored and managed cloud resources. Now, my job is to have a strategic oversight of resources rather than getting caught up in the weeds of day-to-day operations.
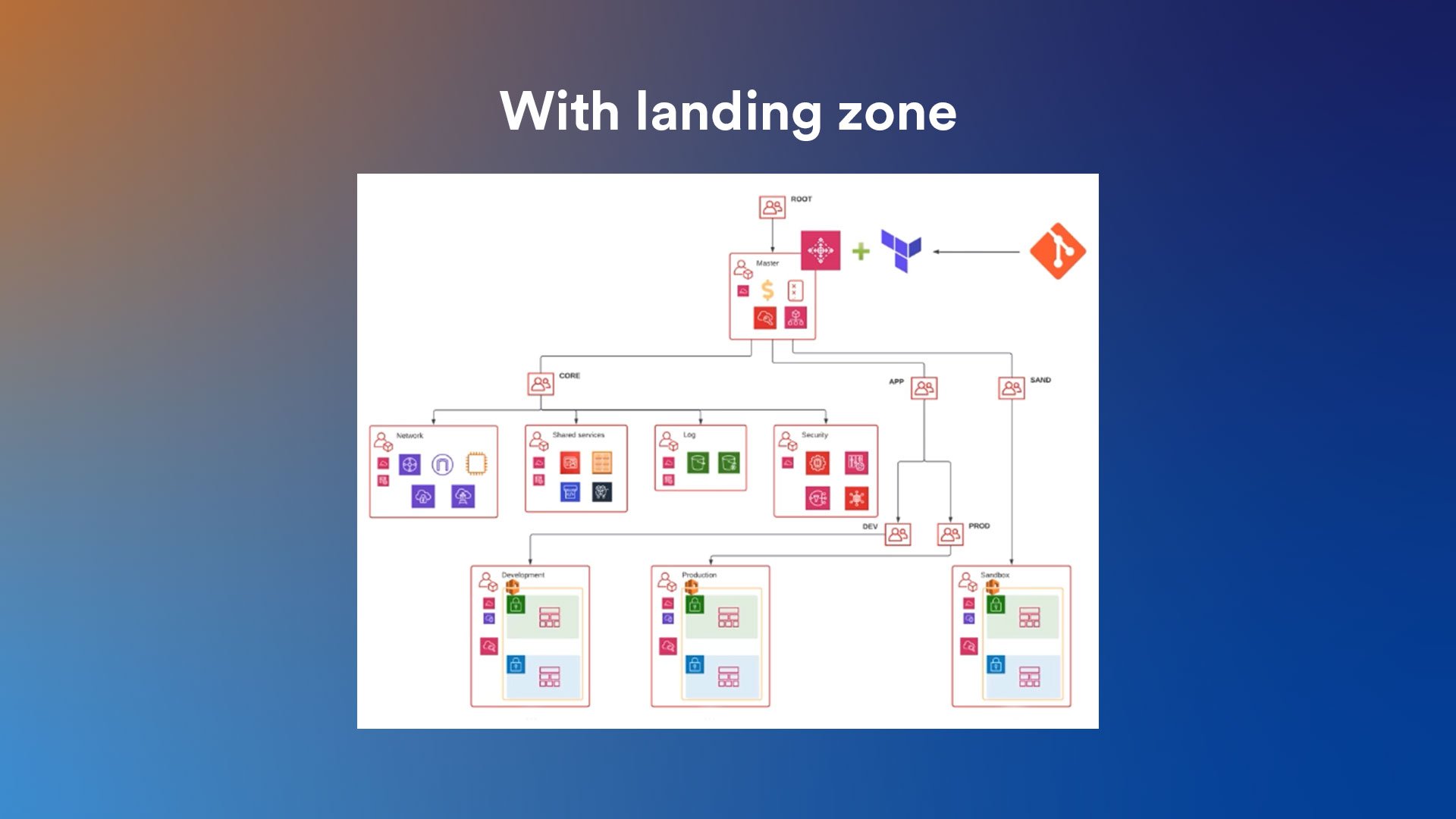
- Blueprints for setup: AWS Control Tower implements a concept called landing zones — pre-configured multi-account AWS environments based on best practices. The blueprints offered by Control Tower simplify environment setup, ensuring all necessary security, logging, and audit configurations are in place from the start.
- Frequent updates: AWS Control Tower releases frequent updates. This means that my cloud environment is always up-to-date with the best practices and compliance requirements, with minimal manual adjustments. This allows me to focus on improving other aspects of our infrastructure and processes, knowing that governance is well-managed.

Space for innovation
AWS Control Tower transformed my day-to-day operations and strategic planning. I spend less time and effort managing AWS accounts. My team was able to focus on innovation rather than maintenance by automating routine tasks and enforcing compliance policies.
Moreover, the unified visibility and control provided by the AWS Control Tower improved our overall security. Automated guardrails and monitoring enabled us to assess and address potential issues proactively, reducing downtime and increasing the reliability of our services.
The shift to a more automated and standardized cloud environment also helped team collaboration. With consistent configurations and governance policies, there was less ambiguity and fewer discrepancies between environments. The handoffs between development and operations became smoother.
For me and my team, AWS Control Tower solved many of the pain points associated with managing a complex cloud infrastructure. Not only did it make our systems more secure, but it also allowed us to focus on the bigger DevOps picture. AWS Control Tower feels like a secret everyone should know.